Publication Date
Is your data really protected?
Data governance and protection are much more than setting up a firewall and two or three information access rules. They are also not a matter exclusive to large organizations.

Every business must have a set of processes and rules in place to ensure the availability, integrity, confidentiality, and traceability of its corporate data.
In addition, with the adoption of An Act to modernize legislative provisions as regards the protection of personal information (c. 25, formerly Bill 64{1} ) in September 2021, data governance and protection are no longer wishful thinking, but a series of obligations with which you must now comply.
Exponential growth in volume of data in circulation
In the e-book “How can Microsoft Information Protection help protect your data wherever it lives{2}?” we learn that the amount of data managed by organizations doubles every two years. What is worrisome is that 54% of organizations report a lack of visibility across their digital estate, and this is amplified by the fact that more than three-quarters have now adopted remote work, at least partially.
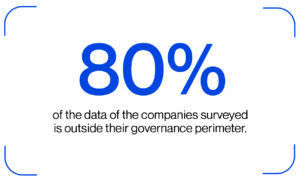
Despite its enormous benefits, remote work has created new problems. In fact, Microsoft notes that the companies surveyed say that 80% of their data is now outside their governance perimeter or can no longer be managed directly. This is alarming.
Every company has four information security objectives: Availability, integrity, confidentiality, and traceability.
Depending on the level of criticality of your data, the risks involved, and the potential impacts, you need to select the appropriate measures to protect yourself.
Data governance and protection are positioned in this arena as the keys to discovering, classifying, and protecting sensitive data, whether dormant or in circulation.
Read also
Information security: Four key goals →
Know your data
You need to understand and be proficient in mapping your data to identify your most sensitive data. This discovery and classification exercise will allow you to order your content, tag it to control where it can go, and protect it appropriately, regardless of its location. It will also help ensure that your data is saved and deleted according to your company’s needs, while respecting the compliance rules that govern your business practices.
Remember that members of your company collaborate with each other, but also with clients and external partners. This means that your content may roam around outside your secure area. You must therefore have the appropriate mechanisms in place to secure this roaming data as well.
Establish confidentiality levels
You must first determine the categories of information you need to protect, then qualify your sensitive data and properly categorize it. You can then choose the confidentiality levels to assign to each category. To this end, you can use confidentiality labels to identify what will be visible to which users with the appropriate rights and restrictions attached.
For example, if you label a document “Confidential – Client,” it could be encrypted automatically, so it can be consulted only by authorized persons. This exercise will allow you to apply the appropriate protection measures based on the required level of confidentiality.
Prevent data loss
You have a multitude of sensitive information under your control, such as financial data, credit card numbers, dates of birth, addresses, etc. You must therefore ensure that users who can legitimately access it cannot share it with unauthorized persons. This process and the tools that support it are called data loss prevention (DLP).
Your data loss prevention strategy allows you to monitor all the actions users take on your sensitive data and to apply the necessary measures if a rule is violated.
For example, if a user tries to copy and paste sensitive information to an unauthorized location, such as an email to an external address, the rule in place can block it from being sent.
The best data loss prevention management tools, such as those provided by Microsoft, can detect the most sensitive data through in-depth analysis of monitored content. They also use machine learning algorithms to detect suspicious activities ever more effectively.
Maintaining control over your data
Governing your data also means identifying the content you need to keep and the content you need to delete. Each piece of data has a lifespan, and you need to determine your retention and deletion strategies based on your business needs. Managing records allows your organization to manage its legal and compliance obligations and comfortably dispose of data that is no longer needed.
From thinking to action
Microsoft offers a range of advanced tools to support your business in implementing data protection governance and management. You get unified management and built-in protection in your Windows and Microsoft 365 environments, which you can extend to applications and other services through connectors. These solutions also allow you to exhaustively identify and classify your sensitive information, using machine learning and other tools.
ITI offers comprehensive services for keeping Microsoft environments secure, including data governance and protection. To learn more, see our section on security.
Are you concerned about the security of your data?
